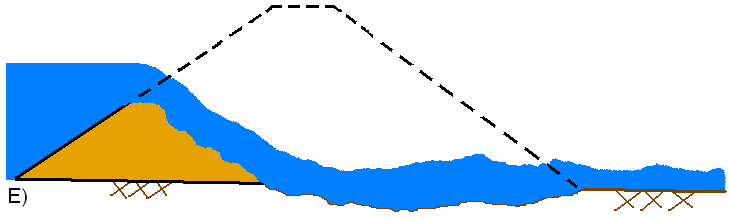
A) Schematic showing key parameters of breach width (Bw) and
By A Mystery Man Writer
Description

Use of structured decision-making to explicitly incorporate
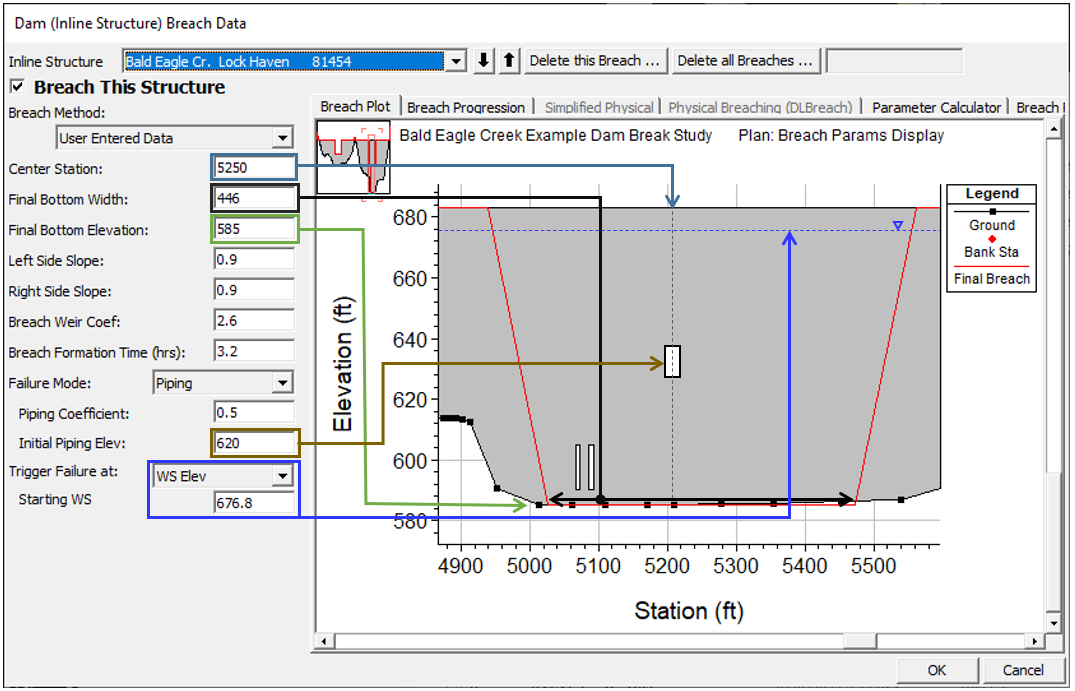
User Enter Breach Data

Experimental methods for local-scale characterization of hydro

Primary ice avalanche starting zones (in red) threatening the assessed
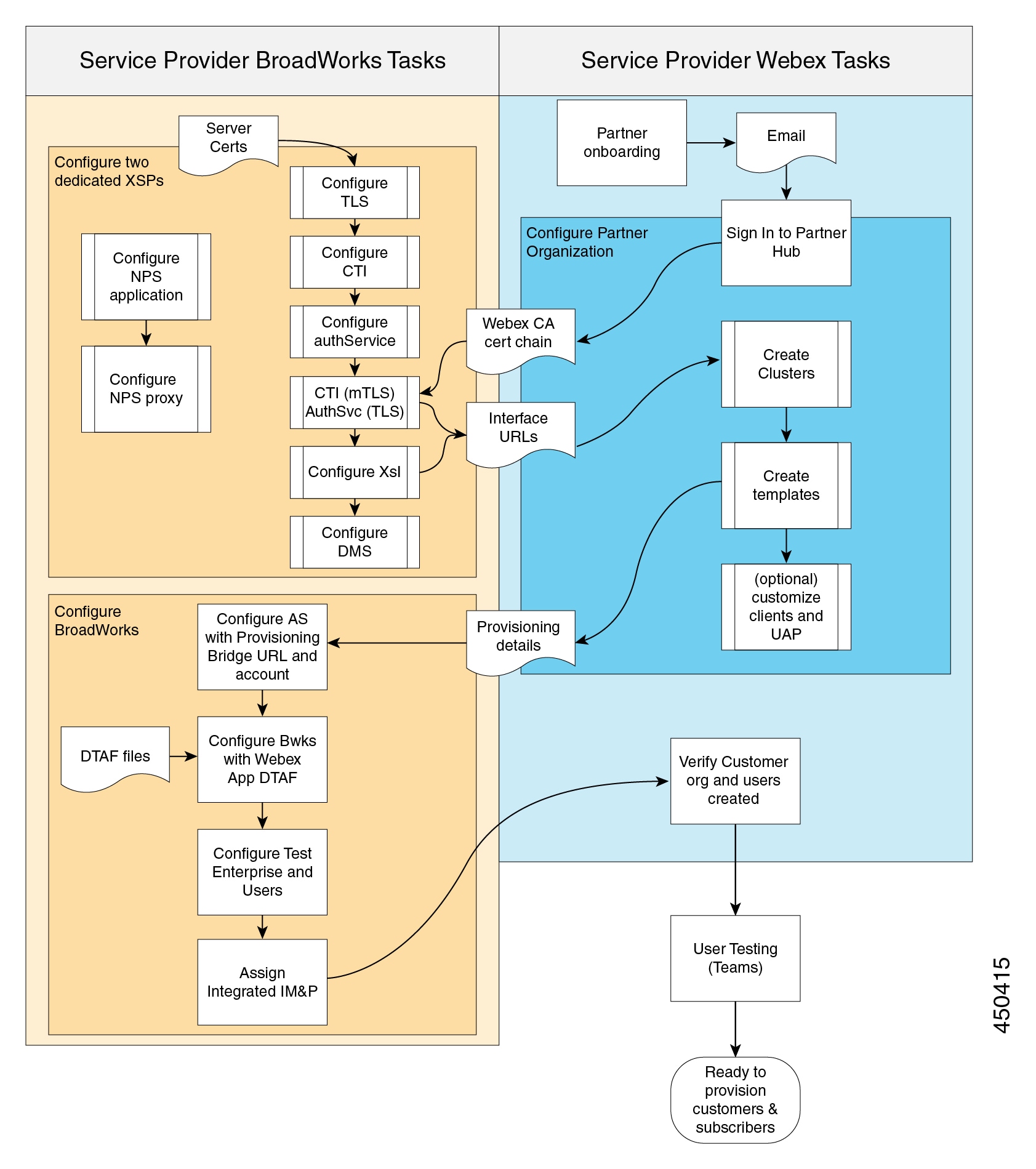
Chapter: Deploy Webex for Cisco BroadWorks

Owen KING, PhD Student, BSc Geography-Geology, MSc Glaciology, University of Leeds, Leeds, School of Geography
Estimating Breach Parameters

Tobias BOLCH, Reader (Associate Professor), PD Dr., University of St Andrews, Saint Andrews, School of Geography and Sustainable Development
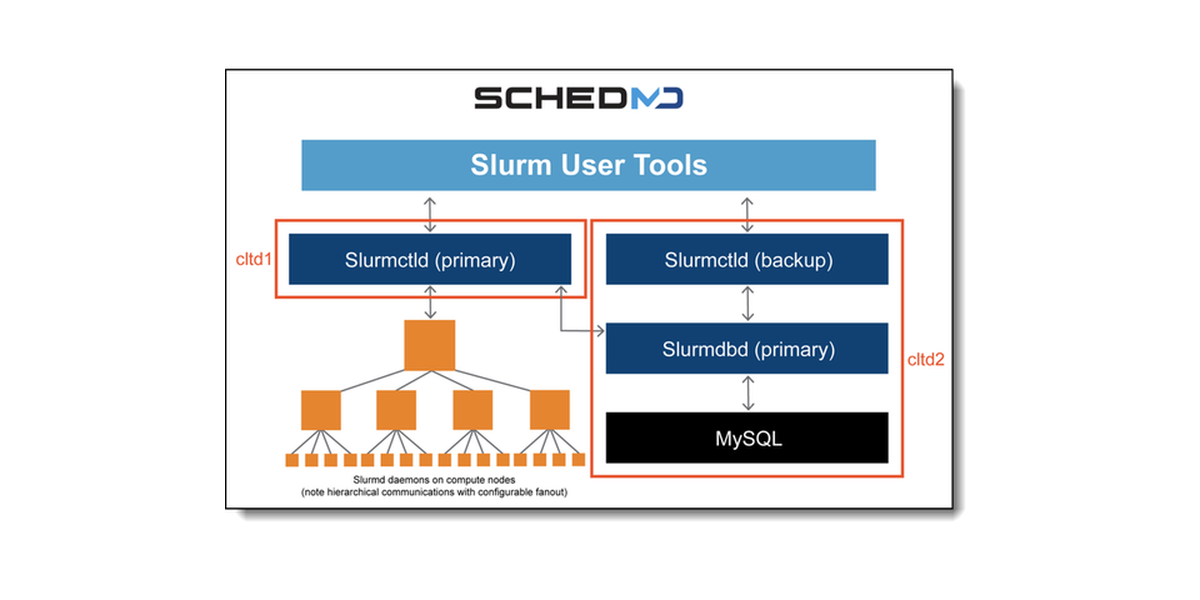
Lenovo Compute Orchestration in HPC Data Centers with Slurm

Ashim SATTAR, Assistant Professor IIT Bhubaneswar; Former Faculty (DST Inspire) @ IISc Bangalore; Former Postdoc @ University of Zurich and Uni. of Dayton, Ohio, USA; Scientific consultant UZH- Mountain Hazards
from
per adult (price varies by group size)